** All courses are also approved for GH, RCFE & STRTP ADMINISTRATORS
BUNDLE & SAVE MORE THAN $100 !!!
After purchase, If you have challenges with your self-paced courses, text +1(626)-484-9256.
CDSS regulations limits the total training hours, an Administrator can take per day to 10 hours .
This includes any combination of different methods of training (i.e. in-person,webinars, virtual, zoom or online courses).
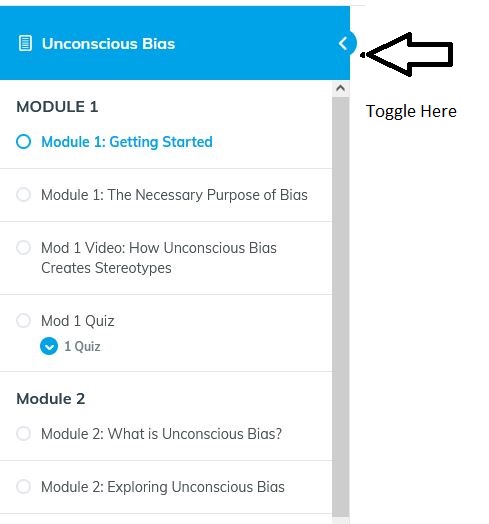
To view all our self-paced (online training) click HERE
TOTAL CEU/Hours in this Bundle: 21
RCFE Administrators:
Dementia is not included in this bundle, swap out 8 hrs worth of courses & take 8 hrs of our Dementia instead. If this applies to you, send us an EMAIL, during the registration process.
ARF Administrators:
4 hrs of HIV/TB is not included in this bundle, you can swap out 4 hours worth of courses & take HIV/TB instead. If this applies to you, send us an EMAIL, during the registration process.
CA Sexual Harassment For Supervisors $39
3 CEU’s *** Laws & Regulations.
** Required by CA Department of Labor
Conflict Management for Supervisors CH 1: The Supervisor & Conflict Management $29
2 CEU’s
Diversity & Inclusion $39
3 CEU’s
Effective Delegation $39
3 CEU’s
Emergency Preparedness – Are You Ready? $ 29
2 CEU’s ***Laws & Regulations
Establishing Employee Expectations $29
2 CEU’s
Food Storage $49
4 CEU’s
Importance of Professionalism in the Workplace $29
2 CEU’s